What Is a Man in the Middle (MITM) Attack?
A man-in-the-middle attack (MITM) is a cyberattack where they secretly inserts themselves into a communication session between two parties.
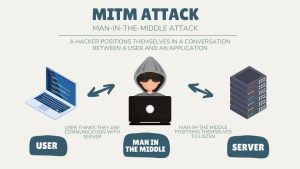
A man-in-the-middle attack (MITM) is a cyberattack where they secretly inserts themselves into a communication session between two parties.

A botnet is a network of devices connected to the internet that has been infected with malware and is controlled as a group by a third party.

From HTML to CSS, JavaScript, and beyond, this web development guide covers helps prepare for the journey and get your projects off the ground.

To be successful in any type of cybersecurity career, here are the three key cybersecurity skills that you must develop to be successful.

Whether you’re looking to get started in the field or are already established, we outline the 7 top types of careers in cybersecurity.

What is cloud computing? In this guide, we’ll look at what cloud computing is, how it works, and the various ways it can help you.

Which cloud computing type is right for you? SaaS vs PaaS vs IaaS – Learn the advantages and disadvantages of the cloud computing types.

We’ll give you a general overview of what it takes to become a cloud engineer. Learn the skills to land your first job as a cloud engineer.

We’ll take you through 5 helpful tips on how to kick-start your career in cybersecurity so that you can get started in a satisfying journey.

While the industry is still relatively new, there are plenty of opportunities for professionals who want to start their cloud computer career.